What is Smishing or SMS Phishing?
Smishing: The Rising Cyber Threat and How to Protect Yourself
In the digital age, cybercriminals are constantly evolving their tactics to exploit vulnerabilities. Among the most insidious forms of cybercrime is smishing, or SMS phishing. Leveraging the ubiquity of mobile devices, smishing attacks aim to deceive individuals into divulging sensitive information or taking actions that compromise their security.
This guide delves into the dangers of smishing, real-world examples, preventive measures, and the latest trends in this growing cyber threat.
Understanding Smishing: The Basics
Smishing is a type of phishing attack conducted via SMS or other text messaging platforms. The attacker poses as a trusted entity to gain a victim's trust, typically urging immediate action such as clicking a link, replying with personal information, or downloading a malicious file.
Smishing is part of a broader category of social engineering attacks that exploit human psychology rather than technological vulnerabilities.
How Smishing Works
- Impersonation: Scammers pretend to be legitimate entities, such as banks, service providers, or government agencies.
- Urgency: Messages create a sense of panic or urgency, pushing recipients to act without thinking.
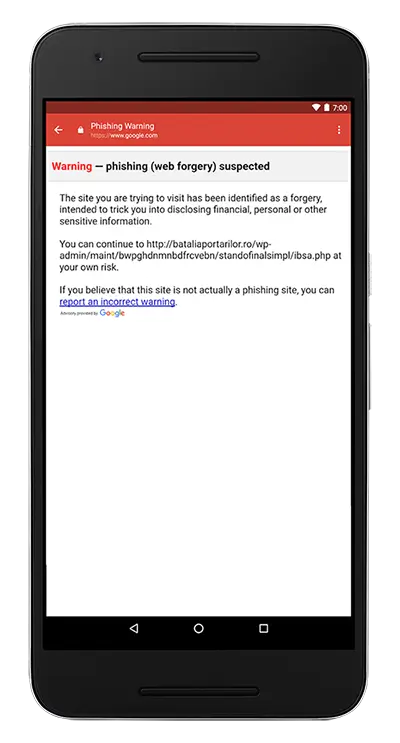
- Execution: Victims who click on links may be redirected to phishing websites or unknowingly download malware that compromises their devices.
Why Is Smishing Dangerous?
As mentioned above, smishing is the act of a scammer to get a person to visit a website or call a phone number in an effort to get that person to reveal sensitive information to the scammer. This can include usernames, passwords, PINs, Social Security Numbers, etc. Alternatively, the scammer could also place malware on the person’s mobile device if the person is asked to visit a website and he/she clicks onto the link in the text message. The malware would then transmit such sensitive information back to the scammer either by finding it on the mobile device or by recording the keystrokes of the person when he/she input the sensitive information on his/her mobile device.
Once the scammer has this information, he can access private accounts of the person to withdraw funds from bank accounts and/or PayPal accounts, make fake credit cards and/or open up new credit card accounts in the person’s name using the sensitive information that has been acquired, etc. In essence, the scammer either wants to steal money and/or commit identity theft so that the scammer can spend money in the person’s name and leave the person to pay the charges.
Why Smishing is Becoming More Prevalent
The prevalence of mobile devices makes them an attractive target for cybercriminals. Here’s why smishing is on the rise:
- Global Smartphone Use: Over 6.9 billion people own smartphones as of 2024, representing nearly 90% of the global population. (Source: Statista)
- Widespread Trust in SMS: Many people perceive text messages as more secure than emails, making them less cautious when interacting with SMS.
- Weak SMS Security: Unlike emails, SMS messages lack robust filtering systems to identify and block phishing attempts.
- Shift to Mobile Banking: With mobile banking on the rise, attackers target users to gain access to financial data.
Real-World Examples of Smishing Attacks
- Banking Scams
- Attackers send messages claiming to be from major banks, warning recipients of suspicious activity on their accounts.
- Victims are directed to click on a link to “secure” their account, leading to phishing websites.
- Delivery Scams
- Popular during the COVID-19 pandemic, these scams inform recipients of a pending package delivery and request payment of customs fees or provide tracking updates.
- Links often install spyware or direct users to fake payment portals.
- Government Impersonation
- Fraudsters impersonate tax agencies, claiming that the recipient owes money or is eligible for a refund.
- These scams often spike during tax season or major events like stimulus check distributions.
Case Study: The Flubot Malware
In 2021, the Flubot malware spread rapidly through smishing campaigns. Victims received messages about missed calls or pending deliveries, prompting them to download a malicious app disguised as a voicemail service. The app granted attackers access to sensitive information on the device, including banking credentials.
The Impact of Smishing
Financial Losses
Smishing is not just a nuisance; it has severe financial implications:
- According to the Federal Trade Commission (FTC), Americans lost over $86 million to text-based scams in 2023 alone, a 30% increase from 2022.
- The average loss per smishing victim is $1,200. (Source: FTC)
Data Breaches
Stolen credentials from smishing attacks often lead to data breaches, exposing victims to identity theft and fraud. Reports indicate that 30% of smishing victims experience secondary breaches due to reused passwords or shared accounts.
Psychological Stress
Victims of smishing often face anxiety and distrust, especially after realizing they have been defrauded. The emotional toll can be significant, impacting overall well-being.
How to Identify a Smishing Message
Recognizing the warning signs of smishing is crucial. Here are some common characteristics of fraudulent text messages:
- Urgency and Fear:
- "Your account will be suspended if you don't act now."
- "You have won a prize! Claim it within 24 hours."
- Generic Language:
- Messages often lack personalization, addressing recipients with terms like “Dear Customer” or “User.”
- Suspicious Links:
- Links may appear shortened (e.g., bit.ly) or mimic legitimate domains with slight variations (e.g., g00gle.com).
- Request for Sensitive Information:
- Legitimate organizations rarely ask for personal or financial details via SMS.
How to Protect Yourself from Smishing
You must become aware that scammers and cybercriminals can easily contact cell phone owners and send legitimate-looking text messages to their mobile devices very easily. You should also be on-guard against any links in any text messages they receive. Since there is no real way to preview the links without tapping on them, you have to be certain that the person who sent it is someone you know and that the person actually sent that text message, since it is relatively easy to change the name of the sender of a message.
To prevent smishing attacks, a you should avoid tapping on any links in any text messages they receive. You can confer with friends if they sent any text messages with links to you before considering tapping on any link.
You should never give out personal information in an online form, through a link, or via a phone number in a text message. In addition, you should never call back any number that is in an unidentified text message.
If you are unsure about the validity of a text message, such as if one’s bank appears to be contacting you via text message and asking to call the bank back, go to the bank’s official website and verify what the phone number is. Alternatively, the you can look on your bank card or on your bank documents to find the number you should call and confirm whether the bank was trying to contact you before responding to an unidentified text message.
You should also consider installing a reputable anti-malware program on your mobile device(s) to prevent malware from getting onto the devices. There are quality anti-malware programs from reputable Internet security companies, including Norton, McAfee, Bitdefender and alike. In additon, Good Internet Security Habits should be should be exercised on a regular basis.
By taking the steps above, you can protect yourself from smishing attacks. This can prevent identity theft and/or the loss of money from scammers trying to access your bank and PayPal accounts using sensitive information they’ve gained through smishing attacks.
Best Practices
- Avoid Clicking Links: If you receive a suspicious message, verify the sender through official channels rather than clicking any included links.
- Report Suspicious Messages:
- Forward the message to 7726 (SPAM) to notify your mobile carrier.
- Enable SMS Filtering:
- Use built-in filters on iOS or Android to block messages from unknown senders.
- Install Security Software:
- Tools like Norton, McAfee, or Avast can detect and block malicious links.
Organizational Measures
Businesses should train employees to recognize smishing attacks, as these scams are increasingly targeting corporate environments.
Learn more about smishing and how to prevent it:
Emerging Trends in Smishing
- AI-Driven Smishing:
- Attackers now use AI to craft personalized messages by analyzing publicly available data, such as social media profiles.
- Smishing as a Service:
- Cybercriminals sell smishing kits on the dark web, lowering the barrier for entry into this type of fraud.
- Voice-SMS Hybrid Attacks:
- Victims receive a fraudulent text followed by a phone call from scammers pretending to be customer service representatives.
Smishing in the News
- International Surge:
- In 2023, smishing attacks rose by 37% in Europe and Asia, where mobile payment apps are widely used.
- A particularly damaging campaign in the UK targeted customers of HMRC, resulting in over £10 million in stolen funds.
- Regulatory Responses:
- Governments worldwide are stepping up efforts to combat smishing. The European Union recently introduced regulations mandating SMS authentication for financial transactions.
How Organizations Can Combat Smishing
While individuals play a critical role in identifying and avoiding smishing, organizations must also take steps to protect their customers and employees:
- Two-Factor Authentication (2FA):
- Require 2FA for sensitive transactions to reduce reliance on SMS-based authentication.
- SMS Sender Verification:
- Implement protocols to authenticate SMS senders, such as Sender Policy Framework (SPF).
- Awareness Campaigns:
- Educate users on recognizing phishing attempts and reporting them promptly.
Conclusion
Smishing is a rapidly growing cyber threat with the potential to cause significant financial and emotional harm. By understanding how smishing works, recognizing its warning signs, and adopting preventive measures, individuals and organizations can protect themselves effectively.
In a digital landscape where cyberattacks are increasingly sophisticated, vigilance and education are the best defenses against smishing. Stay informed, stay cautious, and always verify before you trust.
Sources:
- Statista: Smartphone Penetration Worldwide
- Federal Trade Commission (FTC) Reports
- Cybersecurity Ventures: 2023 Phishing Statistics
- European Union Cybersecurity Agency (ENISA) Reports