Social Engineering Attacks: What They Are, How They Work, and How to Stay Safe
Introduction: The Human Factor in Cybersecurity
No matter how advanced security software becomes, one vulnerability never goes away: people. Social engineering attacks don’t target firewalls or passwords — they target trust, distraction, fear, and curiosity. It’s why a single well-crafted email or phone call can do more damage than a million brute-force login attempts.
Social engineering is the art of manipulating someone into giving up information or access. It’s subtle, low-tech, and incredibly effective — because it bypasses security systems entirely by going straight to the human element.
You don’t need to be a tech expert to understand this threat. In fact, that’s the point: anyone with an email address, phone, or LinkedIn profile is a potential target. The good news? Once you know how these attacks work, they’re much easier to spot and stop.
This article breaks down how social engineering happens, what forms it takes, and how you can stay one step ahead — whether you’re online at home or at work.
What Is Social Engineering?
Social engineering is a form of cyber attack that relies on psychological manipulation instead of hacking tools or code. Instead of exploiting software, it exploits people — getting them to voluntarily hand over sensitive information, click a malicious link, or provide access to secure systems.
These attacks are often the first step in a larger breach. Attackers use them to steal login credentials, install malware, or move deeper into a network. It’s not about breaking in — it’s about being let in.
What makes social engineering so dangerous is that it can take many forms — a fake email from your boss, a tech support call that seems legit, or even someone showing up at the office claiming to be from the IT department.
The tactics may vary, but the goal is always the same: gain trust, bypass defenses, and extract value.
And it works. According to a 2023 report by Purplesec, 98% of cyber attacks involve some form of social engineering. It’s a favorite tool of cybercriminals because it doesn’t require expensive tools — just a convincing story, the right timing, and a little bit of luck.
Understanding how these schemes work is the first line of defense.
Common Types of Social Engineering Attacks
Social engineering attacks take many forms, but they all have one thing in common: they target people, not technology. Here are the most common types, with real-world examples and visual cues to help you recognize them in action.
Phishing
Phishing is the go-to method for attackers because it’s cheap, fast, and effective. The attacker sends a message — usually by email, but increasingly via SMS (smishing), voice call (vishing), or messaging apps — that impersonates a trusted source. These messages often mimic companies like Amazon, Microsoft, or internal departments like HR or IT.
The goal is to get you to click a link, download an attachment, or enter credentials on a fake website. It works because the message usually creates a sense of urgency, fear, or reward, pushing you to act without thinking it through.
📊 Stat: The 2025 Phishing Trends Report found that 80-95% of cyber-attacks begin with a phish. In addition, an increase in phishing attacks since ChatGPT in November 2022 — is a staggering 4,151%.
Case Study: Colonial Pipeline (2021)
A single compromised password — likely stolen via phishing — led to one of the most disruptive infrastructure cyberattacks in U.S. history, halting fuel deliveries and triggering panic buying across the East Coast.
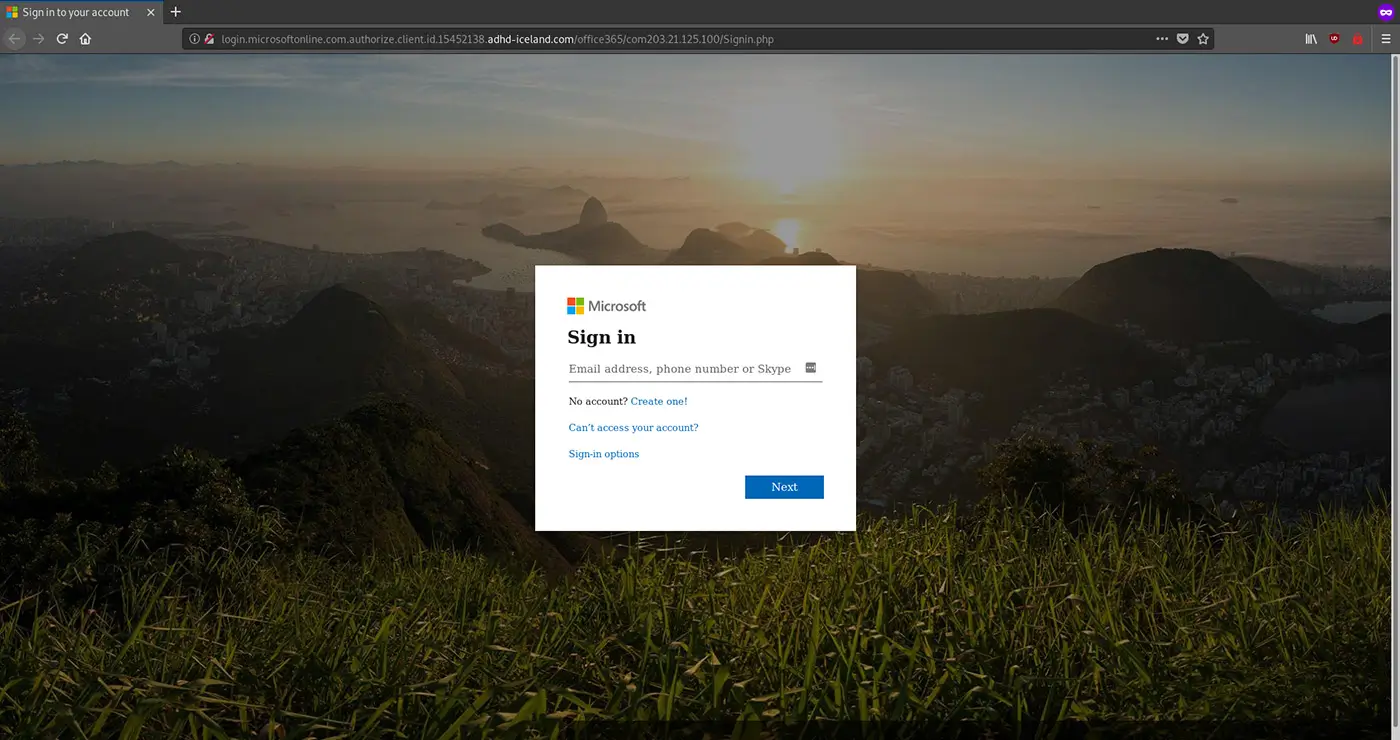
Below is a screenshot showing a fake Microsoft login page. Pay attention to the URL in the address bar. It is not any of the official Microsoft's URLs.
Pretexting
Pretexting is all about the setup. An attacker creates a false identity — an IT admin, vendor, executive assistant, or law enforcement officer — and invents a situation that justifies requesting sensitive information. Unlike phishing, which casts a wide net, pretexting is more targeted and manipulative, often involving direct communication over phone or chat.
These scams succeed when the victim is caught off guard and assumes the attacker is legitimate due to tone, authority, or context.
Case Study: Twitter Hack (2020)
Attackers impersonated internal IT staff and tricked Twitter employees into sharing credentials, ultimately gaining access to admin tools and hijacking high-profile accounts like Elon Musk’s and Apple’s.
Baiting

Baiting is the digital version of leaving a trap. It plays on curiosity, greed, or fear of missing out, offering something enticing — a free download, movie, game, or even a "lost" USB drive left in a public space. But the moment the bait is taken, malware is delivered or the victim is redirected to a malicious site.
What makes baiting dangerous is that the target actively chooses to interact, making it feel like a self-initiated action.
Example: In past penetration tests, security firms have dropped infected USB drives in corporate parking lots — and over 50% were picked up and plugged in.
Tailgating (Piggybacking)

Tailgating happens in physical environments and involves an attacker entering a secure area by simply walking in behind someone with authorized access. They may pose as a delivery person, maintenance worker, or just a fellow employee who “forgot their badge.”
This kind of attack takes advantage of human politeness and social norms, like holding a door open for someone.
Notable Case: Real-World Penetration Test (Shared by Social Engineer LLC)
In a controlled security test, penetration tester Deviant Ollam successfully entered multiple corporate offices just by carrying coffee and saying something casual like, “Sorry, can you hold the door? I left my badge at my desk.”
No hacking tools, no forced entry — just social cues and people’s instinct to be polite.
Quid Pro Quo

In a quid pro quo attack, the attacker offers something in exchange for access — like fake IT support offering to fix a problem if you give them your password or remote access.
These scams work because they seem helpful or transactional. The victim believes they’re getting support, when in fact, they’re giving up control.
Lesson: If you didn’t ask for help, be skeptical when someone offers it out of the blue.
These tactics may feel different on the surface, but the core method is the same: they manipulate emotions — trust, fear, curiosity, urgency — to get past your defenses.
Real-World Examples That Still Matter
Social engineering isn’t theoretical. Some of the biggest and most costly cyber incidents in recent history began with a simple trick, a lie, or a misjudged click. These real-world examples prove how effective social engineering still is — and why awareness is your best defense.
Twitter Hack (2020)
Attackers posed as internal IT staff and contacted Twitter employees, convincing them to hand over credentials to internal admin tools. Once inside, they hijacked major accounts — including Barack Obama, Elon Musk, and Apple — and used them to promote a Bitcoin scam.
🔑 How it started: Pretexting
💸 Damage: Massive reputational harm, public trust eroded
📚 Lesson: Even tech companies with top-tier security can fall to one convincing phone call.
Target Breach (2013)
Cybercriminals gained access through a third-party HVAC vendor, then moved laterally into Target’s payment systems. Malware was installed on POS terminals, resulting in the theft of 40 million credit and debit card numbers.
🔑 How it started: Vendor phishing and poor network segmentation
💸 Damage: $162 million in costs (after insurance)
📚 Lesson: Social engineering doesn’t always target you — it targets your weakest link.
Colonial Pipeline Attack (2021)
One compromised password gave attackers access to Colonial’s network, forcing them to shut down fuel distribution across the U.S. East Coast.
🔑 How it started: Phishing
💸 Damage: Ransom paid: $4.4 million; economic ripple effect far worse
📚 Lesson: The cost of a single credential leak can be national-scale disruption.
💡 Fast fact: The average cost of a data breach in 2023 was $4.45 million — IBM
These aren’t isolated incidents. They’re a pattern — and they all started with someone trusting the wrong message or voice.
Why Social Engineering Works
Social engineering doesn’t rely on technical exploits — it relies on human nature. That’s why it’s so effective, and why it keeps evolving.
At its core, social engineering works because people are predictable. We’re wired to be helpful, curious, and to trust authority. Attackers know this, and they use it to their advantage.
Here are some of the psychological triggers they exploit:
- Urgency – “Your account will be locked in 10 minutes.” People react fast under pressure.
- Fear – Threats of legal trouble, job loss, or account compromise can cloud judgment.
- Curiosity – A file labeled “Salary Breakdown” or “Confidential Strategy” is hard to ignore.
- Trust in authority – Messages that appear to come from a CEO, HR, or IT are rarely questioned.
- Desire to help – Many people fall for scams because they think they’re doing the right thing.
These aren’t flaws — they’re normal human responses. But when combined with stress, distraction, or fatigue, they create the perfect opening for a scam.
The rise of remote work and AI-generated content has only made things worse. It’s easier than ever for attackers to craft convincing messages, fake voices, or simulate trusted systems.
Bottom line: Social engineering works because it targets people, not tech. And people, no matter how smart, can be tricked.
Red Flags: How to Spot a Social Engineering Attack
Social engineering attacks don’t announce themselves. They show up looking helpful, urgent, or totally routine — which is exactly why they work. But there are patterns. Once you know what to look for, the red flags get easier to spot.
Here are the most common warning signs:
🚩 Unexpected Urgency
- “Act now or lose access.”
- “We need this by end of day.”
- Urgency is a classic manipulation tactic. It shuts down critical thinking.
🚩 Strange Sender or Domain
- Email from support@amaz0n-security.com instead of amazon.com.
- Names might look right, but the address doesn’t check out.
🚩 Generic Language
- “Dear user” or “Dear employee” — attackers rarely know your name.
- Real internal emails usually feel personal or specific.
🚩 Suspicious Attachments or Links
- Files you didn’t ask for.
- Hovering over links shows mismatched or shady URLs.
🚩 Requests for Sensitive Info
- Passwords, banking details, 2FA codes, employee records — legitimate companies won’t ask for these by email or chat.
🚩 Too Good to Be True
- Free stuff, exclusive offers, or refunds you weren’t expecting.
If something feels off, pause. Double-check. Ask someone. In social engineering, hesitation is protection.
🔒 Rule of thumb: If you wouldn’t say it to a stranger in an elevator, don’t share it online or over the phone.
How to Protect Yourself and Your Organization
Social engineering isn’t just an IT problem — it’s a people problem. And that means everyone has a role to play in keeping systems, data, and identities safe.
Here’s how to build a solid defense, whether you’re protecting yourself or your whole team.
🔐 For Individuals
- Slow down before clicking. Don’t let urgency push you into reacting. Take a moment to verify.
- Double-check sender info. Look closely at email addresses, domains, and tone. When in doubt, confirm through another channel.
- Use multi-factor authentication (MFA). Even if your password is stolen, MFA adds a second layer.
- Limit what you share online. Attackers use social media to craft convincing scams. Avoid posting things like your job role, vacation plans, or personal contact info.
- Install updates. Software updates fix vulnerabilities that attackers love to exploit.
🛡️ For Organizations
- Train employees regularly. Make phishing simulations and awareness training part of the culture — not just a one-off.
- Implement least-privilege access. Don’t give users more access than they need to do their jobs.
- Use email filtering and endpoint protection. Tools like spam filters, antivirus, and browser protections catch threats before people do.
- Enforce strong password policies. Encourage password managers and require MFA.
- Have an incident response plan. Everyone should know what to do if a scam gets through.
Remember: Technology helps, but people are your first and last line of defense. Make sure they’re ready.
The Role of AI in Social Engineering (and Defense)
Artificial intelligence is changing the game — for attackers and defenders alike.
On the offensive side, AI makes social engineering attacks more convincing and scalable. Scammers can now generate highly personalized phishing emails in seconds, mimic voices using deepfake audio, or create realistic fake images and documents. This makes it harder for the average person to tell what’s real and what’s fake.
One growing threat: AI-generated spear phishing, where bots scrape social media and company websites to tailor messages that feel familiar and authentic.
But AI isn’t just a threat — it’s also a powerful shield. Defenders use AI for threat detection, scanning millions of data points to spot suspicious behavior in real time. AI can flag login anomalies, detect phishing patterns, and even analyze employee response times to potential scams.
The takeaway? AI has raised the stakes — but it’s also raised the bar for defense. Stay informed, stay alert.
Final Thoughts: Stay Alert, Stay Safe
Social engineering attacks aren’t going anywhere — they’re just getting smarter. As long as people are part of the system, attackers will keep trying to exploit human behavior instead of breaking through firewalls.
But you don’t need to be paranoid — just prepared.
By learning the signs, slowing down, and staying skeptical of the unexpected, you make yourself a much harder target. And when organizations back that up with strong policies and regular training, the risk drops even further.
In the end, your brain is your best firewall. Use it.
References:
Cybersecurity Statistics by PurpleSec
2025 Phishing Trends Report by Hoxhunt
New York State, Department of Financial Services: Twitter Investigation Report
U.S. Senate Committee on Commerce, Science, and Transportation: A “Kill Chain” Analysis of the 2013 Target Data Breach (PDF)
TechTarget: Colonial Pipeline hack explained, Everything you need to know
Cost of a data breach by IBM